A canvas in a tool builder application is essential because it provides a visual, interactive, and dynamic space where users can create, manipulate, visualize, and refine their tools, designs, or content. It plays a central role in the functionality and user experience of such applications. Over the course of my career, I've had the privilege of conceptualizing and designing a canvas that empowers users to build and customize widgets while facilitating the development of efficient internal tools.
The challenge here is to use the limited space available and make the most of it. We also faced a ton of challenges. The canvas did not let you overlap widgets, meaning we will need to now play on a linear field. Since we did not have Figma like experience of toggling the menu, we also wanted tot strike a balance where we do no overwhelm the user with options.
Canvas old
Permission control center for the admin. They can granularly set the permission for each user group to a resource.

Canvas new
Problem Statement
Access Control is a fundamental aspect of any system, and two common approaches to implementing it are Attribute-Based Access Control (ABAC) and Role-Based Access Control (RBAC). ABAC focuses on evaluating permissions based on attributes associated with users and resources. We did not want to make it as complex as AWS, Azure and the likes of others, but also wanted the admins to have as much control as they want.
When designing an Access Control system, the designer must navigate through complex states and user flows to ensure security and usability. They meticulously map out user roles and their corresponding permissions, defining what actions each role can perform. Additionally, in the case of ABAC, they identify relevant attributes and conditions that determine access rights.
The designer's challenge lies in striking a balance between security and user-friendliness. They must create a seamless user experience, ensuring that users can easily understand and manage their permissions while still adhering to security protocols. This involves designing intuitive interfaces for role assignment, attribute management, and access policy configuration. Throughout the process, the designer must anticipate various scenarios and potential conflicts to provide a robust and flexible Access Control system that meets the needs of the organization while safeguarding sensitive data and resources. It's a delicate dance of complexity and simplicity, ultimately resulting in a well-designed and secure system.
Canvas and tool builder
Permission control center for the admin. They can granularly set the permission for each user group to a resource.
User management dashboard for show a central repo of all user, permission and user groups
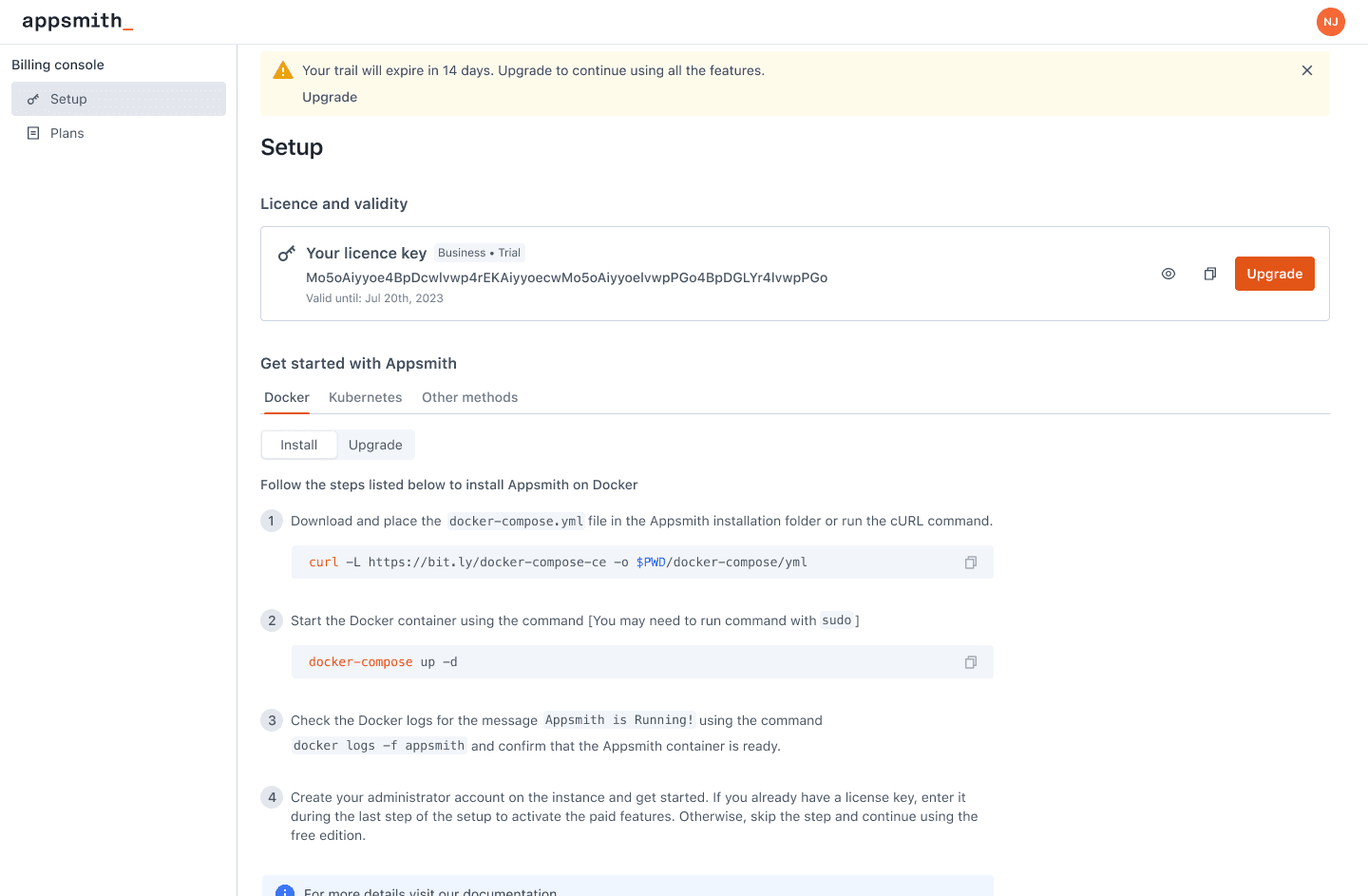
Admin pages to show them license validity and download instructions
Plans page to help the user find the current plan but also nudge them to upgrade.
Problem Statement
Billing and usage, which is a common term in the industry is not so easy to implement when you are working with self hosted instances. These instances are locally running on a VM and they might or might not connect to the internet on a regular basis. Plus they do not behave like an e-commerce setup where you hit add to cart and checkout. These get even more complicated when you are working with licenses and managing them and the system runs into a variety of states like license is over or expired or the user did not pay. Designing flows for these require a lot of time and energy to understand how the different flows will work and still tie them up in a cohesive way so the admins can perform the tasks.
In conclusion